Home » Active Directory Management Tools: Must-Have Features » Active Directory Management: A Comprehensive Guide
Active Directory Management: A Comprehensive Guide
Learn about the best practices for managing Active Directory and how Cayosoft can help with the complex and crucial task of securing and monitoring AD environments.
Explore the chapters:
- Chapter
- Active Directory Management Tools
- Active Directory Group Policy Management
- Active Directory Security
- Active Directory Management
- Active Directory Disaster Recovery
- Active Directory Auditing
- Active Directory Groups
- Disable Active Directory
- Active Directory Reporting
- Active Directory Backup
- Active Directory Forests
- Active Directory Monitoring
- Chapter
- Active Directory Management Tools
- Active Directory Group Policy Management
- Active Directory Security
- Active Directory Management
- Active Directory Disaster Recovery
- Active Directory Auditing
- Active Directory Groups
- Disable Active Directory
- Active Directory Reporting
- Active Directory Backup
- Active Directory Forests
- Active Directory Monitoring
Like This Article?
Subscribe to our LinkedIn Newsletter to receive more educational content
Active Directory (AD) is a victim of its own success. There has never been a more widely adopted user and identity database, but the flip side is that AD management has become incredibly complex and cumbersome if you use the native tools provided by Microsoft.
Over time, as organizations grow and their AD grows with them, permissions creep accumulates, visibility and understanding decrease, inconsistencies between user accounts and other objects accrue, and backups and day-to-day management become increasingly difficult. This all contributes to the challenge of Active Directory management. The stakes are high for the systems administrator managing AD because it is often the key to sensitive information stored inside an organization, making it a prime target for cyberattacks.
In this article, we discuss the best practices of managing Active Directory and how Cayosoft can help you manage various aspects of the user account lifecycle.
Summary of Active Directory Management Best Practices
| Best Practice | Description |
| Secure all AD accounts | Adopt policies and a structure that secures privileged AD accounts. |
| Disable unnecessary and inactive accounts and devices | Don’t leave any inactive accounts or devices enabled that provide a vector for attack. |
| Secure AD with a defense-in-depth approach | Use 2FA, deploy LAPS, and configure access using the principle of least privilege. |
| Always monitor and audit your Active Directory instances | Monitor logs for suspicious activity, health or replication problems, and signs of compromise. |
| Maintain a consistent strategy for monitoring your cloud and hybrid AD instances | Employ a strategy to manage cloud and hybrid AD environments where one-to-one relationships are not always present. |
| Have a recovery plan | Institute a recovery plan that is bulletproof and can be implemented quickly since Active Directory stability is critically important. |
Secure All AD Accounts
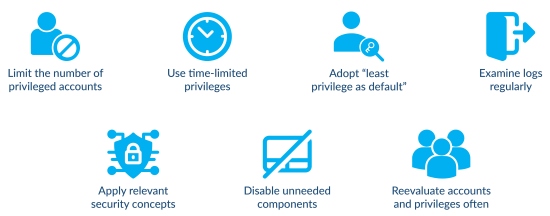
Securing AD accounts is one of the top security priorities for a systems administrator. As with any security operation, there are varying levels of security that are possible to implement, and the level of security has to be tailored to both the type of user and by assessing the tradeoff between organizational risk and ease of use.
The best approach is to only grant user accounts the minimum level of access needed to accomplish their jobs. Known as the “principle of least privilege” among security practitioners, the idea is simple, but the implementation is easier said than done. It often becomes too easy to just add users to an already established AD group to give them access to shared printers or other resources on the network rather than creating a new group with the appropriate level of delegated access for the new needs. Even worse, when there are too many one-off situations, it may become common practice to add single-user permissions to resources like files and folders, which quickly becomes an insecure, unsustainable nightmare.
Manage, Monitor & Recover AD, Azure AD, Office 365

Unified Console
Use a single tool to administer and secure AD, Azure AD, and Office 365

Track Threats
Monitor AD for unwanted changes – detect for security or critical functions

Instant Recovery
Recover global enterprise-wide Active Directory forests in minutes, not days
An undisciplined approach inevitably results in permissions creep, where users gradually accumulate more and more permissions than they need. This poses a threat to the organization if a user account becomes compromised or a user unfortunately does something erroneous (i.e., accidentally deletes a file share) unintentionally or even maliciously.
In addition to securing AD accounts’ access to resources using the principle of least privilege, systems administrators must also create best-practice naming conventions for both accounts and groups so that they can easily track which accounts have access to which resources and quickly identify things in logs. For example, service accounts might all start with the prefix “SVC-” to identify them easily. You may decide that all computer names will start with a prefix denoting their location, such as “LA-01” for the Los Angeles 01 computer vs. “PHX-05” for one in Phoenix.
The administrator in charge of AD will have to delegate some levels of access to other users either within IT (such as helpdesk support) or outside IT (department-based support). This is necessary so that they can have the required levels of access needed to create new users, reset passwords, grant certain levels of access, etc.
Perhaps most important of all is keeping the number of high-power users (e.g., domain admins) as small as possible. This is where the granular delegation of powers becomes key since, without that ability, it becomes too easy to solve problems in the moment by adding people to the admin or domain admin groups, only rarely pulling those permissions back if they are no longer needed. To this end, Cayosoft Administrator offers a self-service portal that can be leveraged to streamline some of these tasks, alleviating some of the pressure that systems administrators face in delegating access to AD.
While the self-service portal is resourceful in empowering users with basic requests and reducing some workload for admins, Cayosoft Administrator offers several features for controlling access via groups:
- Dynamic Groups: Automatically update membership based on predefined rules and user attributes.
- Restricted Groups: Provide manual control over membership, offering heightened security for particularly sensitive groups.
- Certification and Attestation: Allow for scheduled reviews and verifications to ensure group membership remains aligned with security policies and regulations.
All these actions require not only methodical planning but perfect execution. Without perfect adherence to the naming convention, user creation with required AD attributes, application of the principle of least privilege, and appropriate delegation of rights, a few mistakes or shortcuts will compound over time. The result will be that AD is no longer secure, and there are built-in vulnerabilities that could be exploited in the event that a malicious actor gains access. This is the case without even considering the challenges present with managing both on-premises AD and Entra ID in ever more common hybrid scenarios.
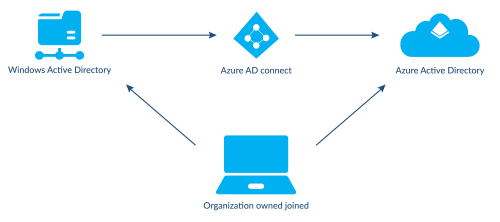
Some of the capabilities and concepts that exist in on-premises AD—such as organizational units (OUs) and delegated access to those OUs—simply don’t have analogs in Azure AD. This means an administrator has to design two sets of policies and delegations of access for on-prem and Azure AD, which becomes almost unmanageable.
Securing AD Accounts with Cayosoft
The native capabilities built into AD and Azure AD simply don’t give enough flexibility to address the challenges described above. Cayosoft Administrator is a part of the Cayosoft suite that focuses on seamless hybrid management of AD and Azure from a single console. Cayosoft AD management and can integrate seamlessly with an existing Active Directory Domain and/or Azure AD tenant. Cayosoft Administrator not only amplifies an administrator’s ability to do things like delegating access, it also streamlines the process and allows one ruleset to be applied to both on-premises AD and Azure (Cloud) AD.
Cayosoft Administrator delivers granular, role-based permission control through a true least-privilege model, automating access and enforcing safeguards (including, but not limited to, naming conventions and object placement). This eliminates the security risks associated with native AD or Entra ID privileges, significantly reducing your attack surface. Its sophisticated rules, policies, and automation capabilities extend far beyond simple OU placement, allowing for highly customizable and flexible solutions.
The Cayosoft Administrator portal offers the ability to design intricate user and group account creation templates that offer granular controls and can use things like pre-programmed regex logic to prevent naming conventions from being violated. Administrators can also automatically assign group membership to users based on specified criteria and OU placement and based on who has been delegated access to create them.
There is substantial value to administrators in using Cayosoft as it seamlessly extends the same least privilege capabilities to Entra ID using the same rules, policies, and automation and within a single instance and console of Administrator. Having this tool gives you tremendous additional power in terms of being able to manage workloads both on your own and via delegation, making it well worth the investment.
Manage, Monitor & Recover AD, Azure AD, M365, Teams
| Platform | Admin Features | Single Console for Hybrid (On-prem AD, Azure AD, M365, Teams) | Change Monitoring & Auditing | User Governance (Roles, Rules, Automation) | Forest Recovery in Minutes |
| Microsoft AD Native Tools | ✓ | ||||
| Microsoft AD + Cayosoft | ✓ | ✓ | ✓ | ✓ | ✓ |
Disable Unnecessary and Inactive Accounts and Devices
Account lifecycle management is one of the more mundane and boring tasks in systems administration and cybersecurity. This is essentially housekeeping, but that means that, unfortunately, it often gets overlooked or even completely ignored. When employees leave—either voluntarily, or in unfortunate circumstances, against their will—someone has to stay on top of deactivating their accounts, removing access to resources and devices, and deleting their data.
In a large company, or even a small but complex one, this can quickly become impossible to manage in a consistent way if an administrator is only using built-in AD tools. First of all, if doing this manually, someone has to keep track of who left and when and must communicate that to the systems administrator or whoever is doing user account management. This must be communicated in a way so that the administrator knows if any data needs to be retained.
For example, if a user leaves but has historically important emails, it may be necessary to retain them. Another user with less sensitive information may be fine to delete immediately. Someone managing this manually is typically unsustainable. Even with the help of in-house ad-hoc PowerShell scripts to automate some of the disabling and deleting is usually effort intensive and error-prone.
Automated Lifecycle Management with Cayosoft
Cayosoft Administrator helps not only with disabling unnecessary accounts but also with all of user account lifecycle management. In addition to having the ability to create custom user creation templates, Cayosoft also can automate the creation of user accounts from an existing source such as a SQL or Oracle database or via a CSV file that can be exported from existing Human Resources software platforms. The creation of user accounts can be done with programmed attributes to support a wide variety of scenarios and customizations.
Cayosoft Administrator’s proprietary method seamlessly automates the creation of AD Only Entra ID Only or Hybrid accounts, including all necessary object creation items such as: mail, licenses, OU placement, attribute completion, and more.
Even more importantly, Cayosoft can automatically manage the deactivation of accounts based on pre-designed criteria pulled from an employee SQL/Oracle database or from a CSV exported from an HR system. This helps keep things in order at all times, enhances security by deactivating accounts as soon as possible, and frees up time for systems administrators to do other, more complex tasks.
Cayosoft Administrator also offers the unique ability to suspend accounts with different policies. The Suspend feature allows the organization to set multiple policies for different scenarios such as regular termination, leave of absence, legal hold, etc. With this feature, administrators can perform all necessary actions such as disabling, removing from groups, clearing attributes, reclaiming licenses, moving to a different OU, etc. Then, if needed, Undo-Suspend will reverse all those actions should the account need to be reactivated.
Watch a 12-minute product demo video of Cayosoft’s hybrid user provisioning
Secure AD With a Defense-In-Depth Approach
Securing AD requires a multi-faceted approach, typically known by cybersecurity practitioners as defense in depth. What this means is that you don’t just use one method—you layer methods on top of each other so that a weakness in one method will hopefully be addressed by another method.
For example, long and/or complex passwords help as a first barrier against brute-force attempts, but if someone steals a password or successfully pulls off a pass-the-hash attack, it renders a long, complex password useless as a defense measure. This is where other layers, like two-factor authentication (2FA) or multifactor authentication (MFA) come into play. With 2FA, a second authentication mechanism is needed to complete an authentication, such as a rotating code or text message. Someone who has stolen a password and entered it to sign into an Azure AD account would also be prompted to enter a text message code sent to the actual user’s phone. The hacker likely doesn’t have access to that phone and would be unable to log in.
2FA is critical to securing on-premises AD and Azure AD. It’s especially important for Azure AD, which is often open to the public internet, whereas on-premises AD traditionally sits behind an organization’s firewall.
Another critical step to securing AD is randomizing the local administrator password on workstations and servers. For a long time, it was common practice to deploy workstations and servers with a single shared local admin password—a practice sometimes still done even now, unfortunately. Hopefully, that password was at least hard to guess! Even more importantly, hopefully, it wasn’t constantly shared with people over the phone, such as users having trouble updating to the latest version of Adobe Reader since they were being prompted for a local admin password.
The reality is that even under tight controls, as employees come and go, the local admin password gets shared with people and gradually becomes less and less secure. It only takes one compromised account and a little bit of privilege escalation for a malicious actor to be able to learn the local admin account. If it is the same on all systems, that person can now access every computer in an organization, wipe all the data, and install ransomware or some other malware.
This is obviously a huge risk. Because this was becoming a major problem, Microsoft released a tool called Local Administrator Password Solution (LAPS) to mitigate it. When LAPS is deployed, an agent is installed on each computer that syncs with the domain controllers and changes the local admin password to a randomized password on a regular schedule. This ensures that each computer has a different, hard-to-guess local admin password and effectively renders attacks against the local admin password futile since learning one will only get someone into that one computer.
Although LAPS works, the problem is getting organizations to deploy it. Administrators don’t like the additional complexity and inconvenience it adds when they are troubleshooting an issue on a workstation, and they often receive pushback from techs in the field who don’t want to deal with the inconvenience. However, the inconvenience is almost always worth the tradeoff since the stakes are so high.
Leverage LAPS and 2FA to Help Secure AD
Cayosoft can help secure AD with both 2FA and LAPS and also adds additional ability to put the principle of least privilege into practice.
Cayosoft can help an organization implement MFA in Azure AD. Specifically, in cases where an organization chooses to not enable MFA for all accounts and use conditional access to enforce MFA on some accounts, Cayosoft gives tools to enforce MFA on certain types of high-powered user accounts and gives insights into which users have turned on MFA. The ideal standard is to turn on MFA for all accounts, but this isn’t always possible in certain organizations.
Cayosoft also has a LAPS tool that is part of the Cayosoft Administrator Web UI AD management portal. It helps administrators and techs more quickly and seamlessly access LAPS passwords for machines and can copy the password to a clipboard for quick remote access. In addition, Cayosoft provides the ability to delegate role-based access to LAPS, tailored to specific admins, and gives the capability to set new expiration dates on passwords.
Even with all these features, mistakes, exploits, and malicious actors can still wreak havoc on AD if they manage to get through these layers of defense. And while it is often true that the best defense is a good offense, sometimes, a good defense is truly having a good defense, which means rock-solid backups.
Cayosoft offers its Guardian suite as a solution for in-depth AD security, monitoring, change management, and backups. It provides the ability to quickly roll back any unwanted or problematic changes instantly, including changes made by unauthorized users. Guardian offers unparalleled monitoring capabilities by monitoring AD event logs and organizing and normalizing the data in a way that is easily manageable by an administrator in the Guardian web UI. In the event of an unauthorized or mistaken change, Guardian gives the ability to quickly and painlessly undo the change with a simple, seamless incremental recovery rather than a full AD restore—which would be high stakes and high stress.
Always Monitor and Audit Your Active Directory Instances
Monitor, Track, and Audit AD Instances with Cayosoft
Maintain a Consistent Strategy for Monitoring Your Cloud and Hybrid AD Instances
The introduction of Azure AD and especially Hybrid AD has brought fantastic features and capabilities to users and organizations for activities like collaboration, remote work, and distance learning. However, the extension of directories into the cloud has also brought with it the problem of significantly expanding the surface area that needs to be monitored.
In hybrid environments, it is a struggle to maintain consistent monitoring between on-premises AD and the Azure AD cloud environment because Microsoft’s native toolset doesn’t provide a single pane of glass for monitoring across on-premises and cloud environments. Trying to accomplish effective monitoring using native tools is difficult, and often there will be a mismatch in terms of capability between on-premises and cloud AD.
Single Point of Administration for On-Prem and Azure AD with Cayosoft
Cayosoft Administrator provides a single point of administration for on-premise AD and Entra ID, giving you granular control over both types of instances in a more uniform way—something that native AD tools cannot do. On-premises AD comes with logical ways of delegating access and assigning permissions such as OUs. Entra ID has Administrative Units which provide some of the functionality of OUs, but are not a one-to-one analogue. Cayosoft helps bridge the gap by providing a method of delegation that allows for the segregation of duties and roles regardless of AD or Entra ID OUs and Administrative Units.
Cayosoft Administrator also provides the ability to provision Microsoft licenses based on configured profiles. This allows for the auto-assignment and revocation of licenses during the lifecycle of a user account.
Have a Recovery Plan
Even the most robust and secure network is vulnerable to some types of catastrophe, and Active Directory is the same. Zero-day attacks for which there are no current countermeasures will always render the best security policies ineffective. Social engineering can circumvent the best spam and antivirus filters, and natural disasters or broken water pipes can thwart even the most robust network design efforts.
This is why it is crucial to have a rock-solid recovery plan in place, especially for Active Directory. It is easy enough to replace a router or a firewall that crashes and upload a new config or even rebuild it from scratch, but the same is not true for AD. If AD crashes or is taken down by malicious actors, rebuilding can be next to impossible. Organizations have gone out of business because of ransomware attacks that took down their AD implementations, so having backups is a must.
By default, AD doesn’t have the recycle bin feature turned on. Assuming it is turned on, deleted objects are available to be restored for a limited amount of time, but if they are recovered, they will lose custom attributes. Recovering from the recycle bin may work for small, single-account issues, but for larger-scale issues, backups will be needed.
It is important to note that the native backup capability for Active Directory makes a full backup. This means that if any changes need to be reverted, all changes must be undone, a fix must be identified, and then all changes need to be redeployed. Although having a backup is far better than not having one, this type of recovery has a significant downside and will inevitably cause downtime to an organization if it ever needs to be used.
Advanced Backup and Recovery with Cayosoft
Cayosoft extends seamless and more advanced backup and recovery strategies for a systems administrator. It provides the ability to create immutable backups that automatically back up to the cloud to protect AD.
Not only does Cayosoft Guardian provide an automated way to back up, it also allows you to implement single-change rollbacks and even provides a level of selectivity that allows you to roll back only the problematic change while keeping any other changes implemented in place. Accounts can be fully recovered back to their original states with all group memberships and custom attributes, and Cayosoft even can recover hard-deleted accounts no longer in the AD recycle bin, with some limitations. Perhaps the most valuable ability is Cayosoft Guardian’s instant forest recovery. It is a unique capability, and Cayosoft is the only vendor that offers it. Forest recovery gives an administrator the ability to establish a healthy working forest in minutes in the event of a full catastrophic failure of AD.
Learn why U.S. State’s Department of Information Technology (DOIT) chose Cayosoft
Conclusion
Managing key aspects of Active Directory can quickly become a difficult task as AD grows in usage, complexity, and the volume of accounts and related objects. Administrators trying to go it alone with ad-hoc PowerShell scripts, unwritten standardization rules, and custom-built utilities will find it increasingly challenging to keep their heads above water. And when an administrator leaves an organization, much of the customization that the admin implemented may not easily transition and could be lost.
To help with these challenges, Cayosoft provides tools to automate the creation of user accounts based on pre-configured rules and manages the entire lifecycle of user accounts, computer accounts, and group objects. In addition, Cayosoft Administrator provides excellent capabilities to delegate role-based access to subordinates, so they can effectively manage user accounts and aspects of AD that pertain to their jobs. Additionally, Cayosoft Administrator greatly enhances the process and capabilities available to organizations and systems administrators for onboarding, lifecycle mgmt, and offboarding of users and groups.
Finally, Cayosoft Guardian provides unparalleled visibility into AD via its monitoring capability that ingests AD event logs. It also provides the ability to back up AD and revert changes in a very granular way. Perhaps most important is the uniformity that the Cayosoft suite of tools brings to managing the entire Microsoft landscape across an organization, spanning both on-premises AD and Azure.
Like This Article?
Subscribe to our LinkedIn Newsletter to receive more educational content