Exchange-related AD group with excessive permissions
Cayosoft Threat Definition CTD-000176
Stop AD Threats As They Happen
Cayosoft Protector provides continuous monitoring and real-time alerts across your entire Microsoft Identity stack
Like This Article?
Subscribe to our LinkedIn Newsletter to receive more educational content
Risk Summary
Excessive permissions granted to Exchange-related Active Directory groups can provide attackers with broad control over critical AD objects, enabling password resets, group membership changes, and full domain compromise.
- Severity: Critical
- Platform: Active Directory
- Category: Exchange, Infrastructure, Privileged Access Management
- MITRE ATT&CK Tactics: Initial Access, Persistence, Privilege Escalation, Defense Evasion, Credential Access
- MITRE D3FEND Tactics: Application Configuration Hardening
Description
Cayosoft Guardian detects a threat when the Exchange Windows Permissions or Exchange Trusted Subsystem security groups in Active Directory have dangerous permissions — such as FullControl, WriteDACL, ForceChangePassword, or AddMember — applied to critical objects (e.g., the domain root).
Inherited via ACLs, these rights allow a compromised Exchange server or admin account to:
- Reset privileged account passwords (including MSOL_* accounts)
- Add accounts to highly privileged groups
- Modify ACLs for full domain control
Many accounts, including Microsoft Entra Connect service accounts, are not protected by AdminSDHolder, leaving them exposed to privilege escalation methods like:
- DCSync attacks
- ESC9 / ESC10 (Exchange permission abuse)
- ESC14 (X.509 certificate mapping abuse)

Real-World Scenario
An attacker gains access to an on-premises Exchange server via a phishing campaign.
By exploiting excessive FullControl and WriteDACL rights inherited by the Exchange Windows Permissions group, the attacker resets the password for an MSOL service account and adds their own account to Domain Admins.
They then modify ACLs to hide these changes from standard admin tools, enabling them to perform DCSync to dump password hashes.
Cayosoft Guardian would detect the suspicious permission assignments before the attacker escalated to full domain compromise.
Stop Privilege Escalation—Then Undo It with Cayosoft Guardian Audit & Restore
Real-time alerts across AD & Entra ID with one-click rollback.
Detect this and other threats with Cayosoft Guardian Protector (Free of Charge)
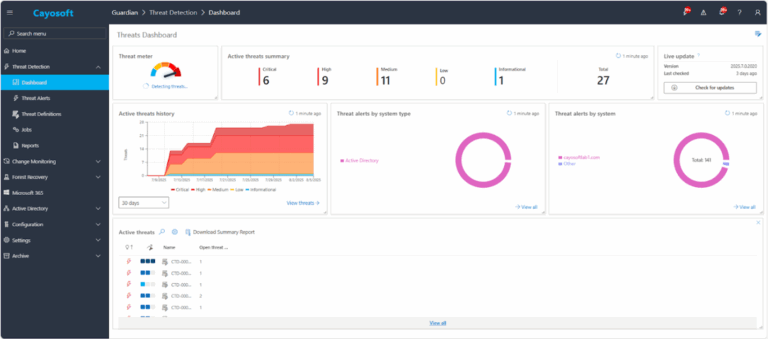
1.) Download Cayosoft Guardian Protector for free real-time threat detection and monitoring of your hybrid AD and Microsoft 365 environment. Once downloaded, sign in and navigate to the Threat Detection Dashboard.
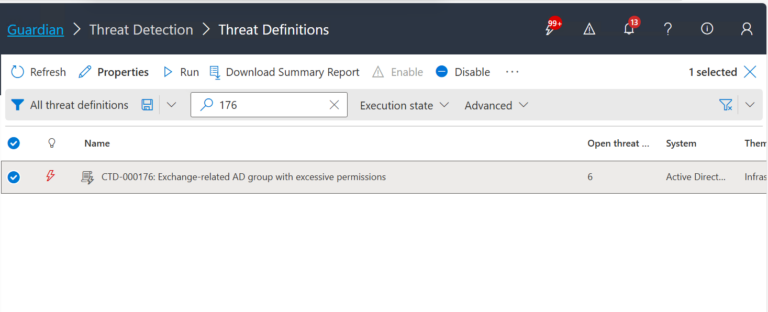
2.) View All Alerts and search for CTD-000176 or “Exchange-related AD group with excessive permissions”.
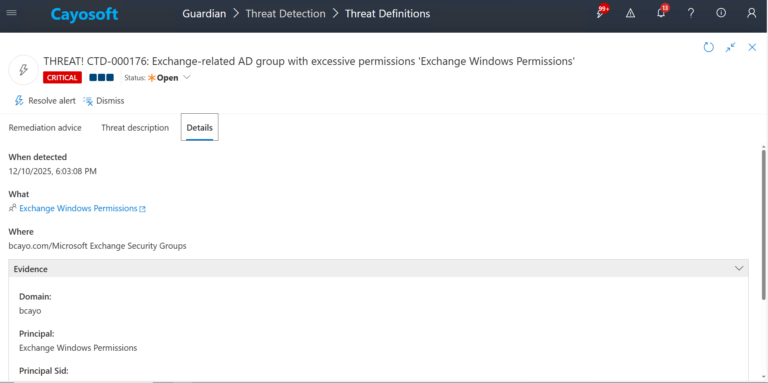
3.) Open any alert and Click for details (from Raise Threat Alert action).
4.) Review the following Evidence fields:
- Domain
- Principal
- Principal Sid
- Permissions
Remediation Steps
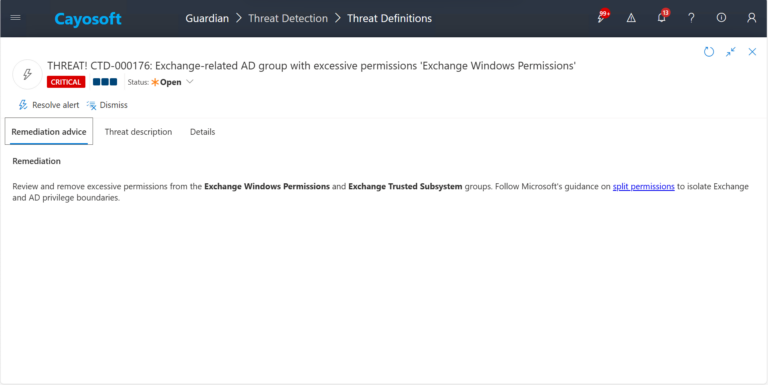
Review and remove excessive permissions from the Exchange Windows Permissions and Exchange Trusted Subsystem groups. Follow Microsoft’s guidance on split permissions to isolate Exchange and AD privilege boundaries.
How to Prevent It
Cayosoft Guardian can proactively detect and alert on Exchange-related AD group with excessive permissions.
It continuously monitors Active Directory, Entra ID, Microsoft 365, and Intune for over 200 misconfigurations, giving early warnings before attackers can exploit them.
FAQ
When groups such as Exchange Windows Permissions or Exchange Trusted Subsystem are granted excessive rights (e.g., FullControl, WriteDACL, AddMember, or ForceChangePassword) on critical Active Directory containers — including the domain root — they effectively gain domain-wide administrative power. A compromised Exchange server or service account can leverage these permissions to reset privileged passwords, alter group memberships, and modify ACLs to conceal activity. This chain of abuse leads to full domain compromise and persistent attacker control without triggering typical account protection mechanisms.
In many hybrid deployments, administrators grant broad rights to Exchange-related groups to ensure synchronization and service functionality between on-premises Exchange, Entra ID (Azure AD), and Microsoft 365. Over time, these rights often remain unreviewed or inherited at the domain or configuration container level, creating excessive privilege exposure. Legacy Exchange installations, manual permission fixes, and incomplete decommissions can further expand this attack surface. Without periodic auditing, these inherited ACLs silently persist across domain upgrades.
Administrators should follow Microsoft’s split permissions model, which separates Exchange administrative permissions from AD domain privileges. Regularly audit and remove unnecessary FullControl, WriteDACL, AddMember, and ForceChangePassword rights from domain-level objects. Limit Exchange permissions strictly to mail-related objects, apply AdminSDHolder protection to critical service accounts where possible, and continuously monitor permission inheritance using tools like Cayosoft Guardian or Microsoft Defender for Identity. This proactive approach reduces lateral movement and prevents Exchange from becoming a privilege escalation vector.
Yes. Cayosoft Guardian Protector provides free detection and alerting for dangerous permission inheritance affecting Exchange-related AD groups.
Yes. Cayosoft Guardian offers continuous monitoring, alerting, full auditing, and prescriptive remediation for Exchange-related AD group with excessive permissions and more than 200 other AD, Entra ID, and Microsoft 365 misconfigurations.
References
Final Thought
Proactive monitoring and timely remediation of configuration risks is essential to maintaining a secure Active Directory and Microsoft 365 environment. By addressing issues like Exchange-related AD group with excessive permissions, you reduce attack surfaces and strengthen your organization’s overall security posture.